Data sovereignty has quietly moved from legal footnote to boardroom priority — and if you work in data governance, it now lands squarely on your plate.
The core idea is deceptively simple: data is subject to the laws and governance structures of the country or jurisdiction where it is collected, processed, or stored. In practice, executing on that principle across distributed cloud infrastructure, multinational operations, and an increasingly aggressive regulatory landscape is anything but simple.
- What Data Sovereignty Actually Means
- Why Data Sovereignty Became a Boardroom Issue
- The Global Regulatory Landscape in 2026
- The Practical Implementation Challenges
- Data Sovereignty and AI: The New Frontier
- Building a Data Sovereignty Framework
- Data Sovereignty in Specific Industry Contexts
- Common Mistakes and How to Avoid Them
- The Strategic Opportunity in Data Sovereignty
- Where to Start: A Practical Action Plan
- The Bottom Line
- Frequently Asked Questions
I have seen this play out firsthand across financial services, federal government, and consumer goods. At Wells Fargo, regulatory pressure around data residency was a constant undercurrent in every infrastructure decision. At the Department of Veterans Affairs, the question of who could access sensitive veteran data — and under which legal authority — was not abstract; it had real operational consequences. At Nestle Purina, managing data flows across global manufacturing and supply chain systems meant navigating a patchwork of national requirements simultaneously.
This guide is written for data governance practitioners, data engineers, and the leaders responsible for enterprise data strategy. We will cover what data sovereignty actually means (not the glossy marketing version), how it differs from related concepts you have probably been using interchangeably, what the regulatory landscape looks like in 2026, the practical implementation challenges nobody warns you about, and how to build a sovereignty posture that survives regulatory change.
What Data Sovereignty Actually Means
Data sovereignty is the principle that digital data is subject to the laws of the nation in which it is collected or processed. It asserts that a government has legal authority over data within its borders — and, in many modern frameworks, over data belonging to its citizens regardless of where that data physically resides.
This is different from what most organizations have been managing. For years, the primary concern was data residency: making sure data was stored within a specific geographic location. Data sovereignty goes further. It is about legal authority, jurisdictional control, and who has the power to compel access, dictate processing rules, and impose liability.
The distinction matters enormously in practice. You can store EU citizen data in an EU data center and still violate data sovereignty if your cloud provider is a U.S. entity subject to the CLOUD Act — because American law enforcement can potentially compel disclosure of that data regardless of where it physically sits. That is a sovereignty problem, not a residency problem.
Residency answers the question: where is the data? Sovereignty answers the question: who actually controls it, and under which legal regime?
A third concept worth separating out is data localization — the requirement that certain categories of data must be stored and processed exclusively within a country’s borders. Localization is the most restrictive expression of sovereignty. Russia, China, and India have all enacted explicit localization mandates for certain data types. Localization is a policy choice; sovereignty is the underlying principle that justifies it.
Understanding all three terms — sovereignty, residency, and localization — and keeping them distinct is a prerequisite for coherent governance conversations. I have sat in too many architecture reviews where these terms were used interchangeably, leading to solutions that addressed residency while leaving genuine sovereignty gaps unresolved.
Why Data Sovereignty Became a Boardroom Issue
Data sovereignty is not new. What is new is the speed and breadth of regulatory enforcement, the geopolitical environment raising the stakes of data control, and the rise of cloud computing creating structural sovereignty risks at scale.
The regulatory acceleration
The regulatory pace has been relentless. GDPR came into force in 2018 and established a high bar for personal data governance in the EU. But GDPR was only the beginning of a global wave. As of early 2026, Gartner estimates that 75 percent of the world’s population operates under some form of modern privacy regulation. The regulatory stack keeps growing.
DORA — the Digital Operational Resilience Act — took effect in January 2025, applying to banks, insurers, investment firms, and critical ICT providers across the EU. DORA links sovereignty directly to operational resilience: regulated entities must ensure that sensitive data and critical processes remain visible and enforceable within the jurisdiction, and that third-party ICT dependencies do not create unacceptable sovereignty exposure.
The EU Data Act became legally enforceable in September 2025. It extends sovereignty beyond personal data to industrial and non-personal data — the sensor output from connected devices, manufacturing telemetry, operational data generated by enterprise IoT. It grants users rights to access and port that data and prohibits vendor lock-in practices that restrict switching. For any organization running connected infrastructure in the EU, the Data Act is a material shift in data rights.
NIS2, the Network and Information Security Directive, was transposed by EU member states through 2024 and entered enforcement in 2025. It extends cybersecurity obligations across energy, healthcare, transport, digital infrastructure, and public administration. From a sovereignty perspective, NIS2 places national authorities in direct oversight of systems underpinning critical functions, linking sovereignty to the resilience of essential services.
The EU AI Act becomes fully applicable on August 2, 2026. It is relevant to data sovereignty because high-risk AI systems — in recruitment, law enforcement, critical infrastructure, and other categories — must maintain activity logs, demonstrate adequate risk assessments, and ensure human oversight. The data those systems consume and produce must be governed accordingly.
Outside the EU, Brazil’s LGPD, India’s Digital Personal Data Protection Act, China’s trifecta of Cybersecurity Law, Data Security Law, and PIPL, and eighteen active U.S. state privacy laws all add to a compliance matrix that any organization operating globally must navigate.
Enforcement is no longer theoretical. Europe has issued over €5.65 billion in GDPR fines since 2018. In 2025 alone, enforcement actions accounted for roughly €2.3 billion — a 38 percent year-over-year increase. Meta was fined €1.2 billion in 2023 for improper EU-to-U.S. data transfers. Google has accumulated hundreds of millions in GDPR penalties. The era of warning letters is over.
The geopolitical escalation
Beyond regulation, the geopolitical environment has made data control a strategic national interest. Governments view data generated within their borders as an economic and security asset. The fragmentation of global data flows is not accidental — it reflects deliberate national policy choices about digital autonomy.
The U.S. CLOUD Act creates a structural tension with EU and Asian sovereignty frameworks. It allows U.S. authorities to compel disclosure of data held by American cloud providers regardless of where that data physically resides. Any organization using AWS, Azure, or Google Cloud — all U.S.-incorporated entities — is exposed to CLOUD Act reach, irrespective of whether their data is stored in Frankfurt, Dublin, or Sydney.
This reality drove the Schrems II judgment, which invalidated Privacy Shield in 2020 and established that Standard Contractual Clauses are not automatically sufficient to protect EU data transferred to the U.S. Organizations must conduct transfer impact assessments and implement supplementary safeguards. The subsequent EU-U.S. Data Privacy Framework provides a current legal mechanism, but it is already under legal challenge and the long-term stability of transatlantic data flows remains uncertain.
France’s decision to replace foreign video conferencing tools with its domestically developed Visio platform is a recent and visible example of sovereign infrastructure as national policy. Germany was among the first countries to develop sovereign cloud initiatives. Across Europe, governments are openly questioning over-reliance on a small number of global cloud providers and pushing for sovereign alternatives.
The cloud architecture problem
Cloud computing solved many problems and created a sovereignty-shaped one. When data was stored in on-premises data centers, its physical location and legal jurisdiction were relatively obvious. Cloud architectures changed that fundamentally.
Data moves across regions for redundancy, latency optimization, backup, and analytics. Multi-cloud and hybrid architectures mean data might touch infrastructure in multiple jurisdictions within a single transaction. Shadow IT means data ends up in cloud services that the governance team never approved. SaaS applications routinely process and store data in jurisdictions their enterprise customers have never mapped.
The result is that most organizations do not have an accurate picture of where their data actually is, which laws apply to it, and who can legally access it. Building that picture — and keeping it current — is the foundational data sovereignty challenge.
The Global Regulatory Landscape in 2026
Navigating data sovereignty means navigating a fragmented, fast-moving set of national and regional frameworks. No two are identical. Here is a practitioner’s view of the major regimes.
European Union
The EU has the most mature and comprehensive data sovereignty framework, anchored by GDPR but now substantially expanded. The current EU sovereignty stack includes:
GDPR establishes personal data protection as a fundamental right and extends its reach beyond EU borders through extraterritorial applicability. Any organization processing EU residents’ data, regardless of where that organization is established, must comply. GDPR makes sovereignty less about physical storage and more about legal authority — EU data must remain governed by EU law, wherever it resides.
The EU Data Act (effective September 2025) redefines sovereignty to cover industrial and non-personal data. It introduces rights for users to access and port data generated by connected devices, prevents vendor lock-in, and gives businesses the right to switch cloud providers without disproportionate cost. For data governance teams, this creates new obligations around data portability and contract management.
DORA applies to financial entities and their critical ICT providers. It requires that outsourcing arrangements give regulated entities full audit rights and contractual control over their data, that concentration risk from over-reliance on any single ICT provider is assessed and managed, and that incident response and data recovery capabilities are demonstrably sovereign.
NIS2 extends cybersecurity and sovereignty obligations across critical sectors with management-level liability.
The EU AI Act (fully applicable August 2, 2026) adds risk-based data governance obligations for AI systems in high-risk categories.
The combined effect is a layered sovereignty architecture that applies to different data types, different sectors, and different risk levels. Operating in the EU now requires a systematic map of which regulations apply to which data and which systems.
United States
The U.S. federal landscape remains fragmented. There is no single federal privacy law comparable to GDPR, though federal sector-specific frameworks — HIPAA for healthcare, GLBA for financial services, FedRAMP for federal government — create meaningful obligations.
The CLOUD Act is the dominant sovereignty instrument at the federal level, establishing the principle that U.S. law can reach data held by U.S. providers regardless of location. CMMC 2.0 creates data sovereignty requirements for defense contractors, requiring that controlled unclassified information be processed on sovereign-compatible infrastructure.
Eighteen state privacy laws are now active, led by California’s CCPA and CPRA. California’s Privacy Protection Agency has shifted to active enforcement, issuing significant fines in 2025. Virginia, Colorado, Connecticut, Texas, and a growing list of other states have enacted their own frameworks. While most follow a broadly similar structure, the differences in consent requirements, sensitive data categories, and opt-out mechanisms create real compliance complexity for organizations operating nationally.
China
China has erected the most comprehensive data localization regime outside the EU, through three interlocking laws: the Cybersecurity Law, the Data Security Law, and the Personal Information Protection Law (PIPL). Together they require that certain categories of data — personal information, “important data,” and data generated by critical information infrastructure — be stored and processed within China. Cross-border transfers require government approval, security assessments, or standard contracts. The regime applies to both domestic organizations and foreign companies processing data in China.
Didi Global’s forced removal from app stores and heavy financial penalties after violating China’s cybersecurity law in 2021 demonstrated that enforcement is real and consequential.
Brazil and India
Brazil’s LGPD, modeled closely on GDPR, establishes comprehensive personal data protection obligations with cross-border transfer restrictions. India’s Digital Personal Data Protection Act, finalized in 2023 with implementation underway, places limits on cross-border transfers and creates new rights for data principals. Both markets are significant enough that multinational organizations cannot ignore them.
Japan and other APAC jurisdictions
Japan amended its Act on the Protection of Personal Information to strengthen rules for third-country transfers, including disclosure and ongoing monitoring obligations. Australia has strengthened its Privacy Act enforcement. The APAC region overall is tightening, with fewer jurisdictions treating data as genuinely borderless.
The Practical Implementation Challenges
This is where many data sovereignty conversations go sideways. Organizations treat sovereignty as a compliance checkbox: determine where data is, make sure it stays there, document it. That approach fails, repeatedly, because the real challenges are architectural, operational, and organizational.
Data mapping at scale
You cannot govern what you cannot see. Effective data sovereignty starts with a comprehensive, accurate, and continuously maintained map of your data: where it originates, where it is stored, where it is processed, who has access, and which legal regimes apply.
In practice, this is extremely hard. Enterprise data ecosystems are complex, distributed, and constantly changing. New SaaS applications get provisioned without governance review. Data pipelines replicate data across regions. Third-party integrations move data in ways that are poorly documented. Shadow IT exists in every organization.
I have worked through data mapping exercises at scale, and the consistent finding is that organizations underestimate both the volume of their data and the number of jurisdictions it touches. What looks like a straightforward EU data residency requirement frequently unravels when you discover that the analytics platform your marketing team is using processes that data in the U.S.
The technology answer here involves data cataloging tools — Collibra, Alation, Informatica — that can automate discovery and classification, combined with robust metadata management that tags data with its origin jurisdiction and applicable regulatory regime. The governance answer involves data stewardship processes that bring new data flows through a sovereignty review before they go live, not after.
Cloud complexity
Public cloud infrastructure creates sovereignty exposure that is architectural in nature, not just a configuration problem. Multi-region architectures, cross-region replication, cloud provider terms of service regarding data access, and the extraterritorial reach of cloud provider home-country law all create sovereignty risk that cannot be resolved by simply selecting a regional data center.
Sovereign cloud options are emerging to address this. AWS European Sovereign Cloud, Azure’s EU Data Boundary, and various national cloud initiatives offer architectures specifically designed to limit data access by non-EU personnel and provide greater assurance against CLOUD Act exposure. These solutions come with real tradeoffs in feature availability, performance, and cost.
A growing number of enterprises are repatriating data from public cloud back to on-premises or hybrid environments — not because cloud is inherently bad, but because the sovereignty risk profile of certain data categories justifies the operational overhead. This is not a reversal of cloud strategy; it is a more nuanced approach that recognizes that different data types have different sovereignty requirements.
Organizations need a data classification framework that explicitly incorporates sovereignty risk as a classification dimension. The highest-risk categories — personally identifiable information subject to GDPR, data covered by DORA for financial services, controlled unclassified information for defense contractors — require different infrastructure choices than aggregate operational analytics.
Third-party and supply chain risk
Data sovereignty obligations flow through your supply chain. Your organization’s commitment to keeping EU personal data within the EU is only as strong as your weakest vendor’s infrastructure. Every data processor in your supply chain — your CRM provider, your marketing automation platform, your HR system, your backup vendor — needs to be assessed for sovereignty compliance.
This is a significant contractual and operational challenge. Standard vendor contracts are not written with sovereignty in mind. Data processing agreements need to address not just data residency but legal jurisdiction, audit rights, incident notification, and what happens if the vendor is subject to a foreign government’s disclosure demand.
Sub-processor chains add additional complexity. Your SaaS vendor may itself rely on a cloud provider whose home-country law creates sovereignty exposure. Mapping sub-processor chains to the required depth is tedious but necessary for genuine sovereignty compliance.
Cross-border transfers
Even with a well-defined sovereign architecture, data flows across borders for legitimate business reasons: customer service operations, shared analytics platforms, global reporting hierarchies. Managing those transfers in compliance with applicable law is operationally complex.
The EU’s regime for cross-border transfers requires either an adequacy decision (the destination country provides equivalent protection), Standard Contractual Clauses with transfer impact assessments, Binding Corporate Rules, or one of a limited number of derogations. The EU-U.S. Data Privacy Framework provides the current mechanism for EU-to-U.S. transfers involving participating organizations, but it is subject to legal challenge.
Transfer impact assessments — which require you to evaluate whether the legal framework in the destination country actually protects the data in practice — are not trivial. They require legal expertise and a genuine understanding of the destination country’s surveillance laws, access mechanisms, and enforcement environment.
Legacy systems
Legacy systems are a pervasive sovereignty challenge. Systems built before modern sovereignty frameworks often do not support the data classification, access controls, regional routing, or audit logging that sovereignty compliance requires. Upgrading or replacing them is expensive; documenting compensating controls and workarounds is operationally painful.
At the VA, systems were routinely decades old, carrying data in formats that predated modern metadata standards. Getting sovereignty-relevant metadata attached to that data was a major project, not a configuration change. This is a common reality in regulated industries, federal government, and any organization that has been through acquisitions and the accompanying IT debt.
Data Sovereignty and AI: The New Frontier
The intersection of data sovereignty and artificial intelligence is where the most complex new challenges are emerging, and it is where governance practitioners need to sharpen their focus.
AI systems consume data at scale across organizational and geographic boundaries. They learn from training data, operate on inference data, and generate output data — each of which may be subject to different sovereignty frameworks. The opacity of many AI systems makes it difficult to determine what data was used, where it was processed, and who had access.
The EU AI Act, fully applicable in August 2026, imposes specific governance obligations on high-risk AI systems. Those systems must maintain activity logs, demonstrate adequate risk assessments, and ensure human oversight. The data those systems use must be governed in compliance with applicable data protection law — which, for any AI system processing EU personal data, means GDPR applies.
The combination of GDPR and the AI Act creates a sovereignty-aware AI governance requirement: organizations must be able to demonstrate that their AI systems process data lawfully, that training data was collected with appropriate legal basis, that personal data is not retained beyond necessary periods, and that individuals’ rights (including the right not to be subject to purely automated decision-making) are respected.
Federated learning and privacy-enhancing technologies (PETs) like homomorphic encryption and differential privacy are gaining traction as approaches that allow AI model training and inference across sovereign boundaries without moving the underlying data. These are not mature technologies for most enterprise use cases yet, but they represent the architectural direction for sovereignty-compliant AI.
The practical implication for governance teams today is to ensure that AI projects go through sovereignty review as part of their design process — not after deployment. Questions to answer before an AI project goes live: What data does it train on? Where is that data sourced and stored? What personal or sensitive data is involved in inference? Where does inference happen? Who can access the model and its outputs? Does the system create sovereignty obligations in jurisdictions where it operates?
Agentic AI systems — AI that takes autonomous actions, manages data, and interacts with external systems — raise additional sovereignty questions around accountability and auditability that governance frameworks are still catching up to.
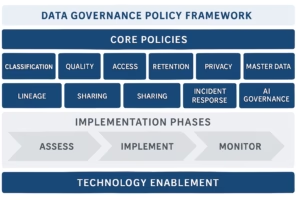
Building a Data Sovereignty Framework
Organizations that survive and thrive in this environment are not those that react to each new regulation as it arrives. They are the ones that have built sovereignty into their architecture and governance processes as a design principle.
Here is how to approach that systematically.
Establish sovereignty as an architectural requirement
Data sovereignty should be embedded in architectural standards, not bolted on as a compliance afterthought. This means that every new data pipeline, every new application, every new cloud service, and every new vendor relationship is evaluated for sovereignty implications before it is approved.
In practical terms, this requires an architecture review process that includes sovereignty checkpoints. It requires data stewardship roles that have the authority and the knowledge to conduct those reviews. And it requires a data classification framework that makes sovereignty-relevant distinctions explicit and actionable.
The classification framework needs to answer, for every data asset: Which jurisdiction’s law applies? Are there localization requirements? Are there cross-border transfer restrictions? What access controls are required? What audit logging is required? The answers drive infrastructure decisions.
Build and maintain a comprehensive data map
You need an accurate, continuously maintained inventory of where your data is. This is foundational. Without it, sovereignty compliance is impossible to demonstrate and impossible to assure.
Data cataloging platforms — Collibra, Alation, Informatica, Microsoft Purview — can automate significant portions of discovery and classification. But technology alone is not sufficient. The governance processes that ensure new data flows are registered, that metadata stays current, and that data map exceptions are tracked and resolved are equally important.
In my experience, the governance process discipline is harder to sustain than the technology. Data catalogs go stale when the processes that maintain them are not embedded in day-to-day operations. Data stewardship that is treated as an add-on to existing roles, rather than a core responsibility, degrades over time.
Data classification should explicitly tag each asset with its sovereignty profile: originating jurisdiction, applicable regulatory frameworks, storage requirements, transfer restrictions, and access restrictions. That metadata then drives automated policy enforcement wherever possible.
Design for sovereignty in cloud architecture
Work with your cloud provider and architecture team to design infrastructure that reflects your sovereignty requirements. This means:
- Using data residency controls that pin data to specific regions, and testing those controls to confirm they work as expected
- Evaluating sovereign cloud options for high-sensitivity data categories
- Using dedicated instances rather than shared infrastructure where sovereignty requirements demand it
- Implementing customer-managed encryption keys so that data is encrypted with keys you control, limiting cloud provider access
- Reviewing cloud provider terms of service for data access rights and government disclosure obligations
- Building contractual sovereignty protections into cloud agreements, including audit rights and incident notification requirements
The EU Data Act’s portability and anti-lock-in provisions are relevant here. Architects should be designing for portability — the ability to move data and workloads between providers — as a sovereignty feature, not just a vendor negotiation tactic.
Implement robust vendor and supply chain governance
Every data processor in your supply chain is a sovereignty risk. Your vendor management program needs a sovereignty dimension.
New vendor onboarding should include a data sovereignty assessment: Where will our data be stored? Under which legal regime? Who has access? What controls prevent unauthorized government access? What are your sub-processor relationships? What are your contractual commitments on data residency?
Existing vendor contracts should be reviewed against current sovereignty requirements. Many were written before DORA, the EU Data Act, and current GDPR enforcement standards, and they do not contain adequate sovereignty protections. Negotiating those protections in is painstaking work, but it is necessary.
For critical vendors, sovereignty assessments should be ongoing, not one-time. Vendors change their infrastructure, update their sub-processor relationships, and get acquired by entities in different jurisdictions. Periodic reassessment is required.
Establish cross-functional sovereignty governance
Data sovereignty is not a technology problem, a legal problem, or an IT problem alone. Effective sovereignty governance requires sustained coordination across legal, compliance, IT, data engineering, business operations, and executive leadership.
Organizations that are doing this well have established dedicated sovereignty teams — cross-functional groups that include legal, security, IT, and business stakeholders — that own the sovereignty compliance program, track regulatory changes, and oversee implementation initiatives.
This is not a committee that meets quarterly to review a status report. It is an operational team that is embedded in the processes by which new data flows get approved, new vendors get onboarded, new architectures get reviewed, and regulatory changes get assessed and incorporated.
Data governance frameworks that treat sovereignty as one regulatory requirement among many — to be addressed when a new regulation arrives and otherwise left to legal counsel — will consistently fall behind. Sovereignty governance needs to be proactive and embedded, not reactive and episodic.
Build for regulatory change
The regulatory landscape will not stabilize. The pace of new legislation and new enforcement activity shows no sign of slowing. Organizations that build their sovereignty programs around the specific requirements of today’s regulations will find themselves in constant catch-up mode.
Build for principles, not just rules. The underlying principles — know where your data is, minimize unnecessary data flows across jurisdictions, implement proportionate controls for sensitive data, maintain audit trails, honor data subject rights — remain consistent even as specific regulatory requirements change.
Build for auditability. The ability to demonstrate compliance — to produce records showing where data was, who accessed it, what controls were in place, and when they were effective — is as important as the controls themselves. Regulators are asking for evidence, not just assertions.
Build for adaptability. Your data architecture should be able to accommodate new residency requirements, new transfer restrictions, and new consent mechanisms without requiring wholesale re-engineering. This means avoiding hard dependencies on specific data locations wherever possible, designing data pipelines to be configurable rather than hard-coded, and maintaining data portability as a design goal.
Data Sovereignty in Specific Industry Contexts
Sovereignty plays out differently depending on your sector. Here are the most relevant contexts for practitioners I commonly work with.
Financial services
Financial services operates under the densest sovereignty-related regulatory stack: GDPR for personal data, DORA for operational resilience, sector-specific data security requirements, and national financial regulatory requirements that often mandate data sovereignty in domestic-currency transaction processing and customer account data.
DORA is particularly significant. It requires that financial entities maintain full contractual control over their ICT outsourcing arrangements, including explicit sovereignty protections. Audit rights, incident notification, and concentration risk management obligations all have sovereignty implications. Financial institutions that outsource critical functions to cloud providers need to renegotiate contracts to meet DORA standards — a significant program of work that many institutions are still completing.
For U.S. financial institutions, FedRAMP, OCC guidance, and state banking regulations layer additional sovereignty-adjacent requirements. The intersection of U.S. and EU requirements for banks operating in both markets is particularly complex.
Healthcare
Healthcare data is among the most sovereignty-sensitive data categories in every jurisdiction. HIPAA in the U.S. imposes data security and disclosure requirements with sovereignty implications. GDPR treats health data as a special category requiring explicit consent and stricter safeguards. Other national frameworks similarly treat health data as high-sensitivity.
Health data sovereignty is further complicated by the growth of digital health, wearables, and connected medical devices — all generating health-adjacent data that may or may not fall under health data regulations, depending on jurisdiction. The EU Data Act’s treatment of connected device data has significant implications for medical device manufacturers and health system operators.
Cross-border clinical research, which involves transferring health data across jurisdictions, requires careful sovereignty analysis. The legitimate interests basis and research derogations available under GDPR must be documented and defensible.
Federal and public sector
Federal government data is subject to sovereignty requirements by definition — government data must typically be processed on government-controlled or government-authorized infrastructure. FedRAMP provides the U.S. federal government’s framework for cloud authorization, and it has explicit data sovereignty dimensions: data must be processed within the U.S., by U.S. persons, with controls limiting access by cloud provider personnel.
The VA context is illustrative. Veteran data includes healthcare information, benefits information, and military service records — all sensitive, all subject to stringent access controls, and all required to remain within U.S. jurisdiction. Cloud adoption at federal agencies has been gradual precisely because sovereignty requirements raise the bar for acceptable infrastructure.
International equivalents — UK G-Cloud, EU institutional cloud requirements, national government cloud initiatives — follow similar patterns of government-specific sovereignty requirements as a baseline.
Manufacturing and industrial
Manufacturing and industrial organizations increasingly face sovereignty requirements for operational technology (OT) data: sensor readings, production telemetry, process control data. The EU Data Act is directly relevant here — it establishes rights over data generated by connected machines and industrial equipment that most manufacturers are only beginning to grapple with.
Supply chain data — which flows across numerous organizations and jurisdictions in complex global supply chains — creates intricate sovereignty challenges. Sharing production data with a tier-one supplier in one country, which shares planning data with a tier-two supplier in another country, which processes it on cloud infrastructure in a third country, creates a data sovereignty trail that is difficult to map and manage.
Industrial espionage concerns add national security dimensions to OT data sovereignty that are not present in consumer data contexts. Several governments have enacted or are considering legislation specifically addressing sovereignty of industrial and strategic technology data.
Common Mistakes and How to Avoid Them
In practice, data sovereignty programs fail in predictable ways. Here are the patterns I have seen repeatedly.
Treating residency as sovereignty. Storing data in a local data center does not make it sovereign if the cloud provider, the SaaS vendor, or the sub-processor is subject to foreign law with extraterritorial reach. Sovereignty analysis has to go beyond the physical storage location to the legal jurisdiction of every entity that can access the data.
One-time compliance assessments. Data sovereignty is not a project that ends. Regulations change, vendor relationships change, data architectures change, and the threat environment changes. Organizations that conduct a sovereignty assessment, document the findings, and then return to business as usual will find their compliance posture decays rapidly.
Siloed implementation. Legal tracks the regulations. IT implements the controls. Neither talks consistently to the other. Business operations proceed without sovereignty constraints. This organizational fragmentation produces documentation that does not match operational reality. Sovereignty governance requires genuine cross-functional integration.
Underestimating supply chain depth. Direct vendor relationships are assessed; sub-processor chains are not. Many sovereignty violations occur in the supply chain, not in the organization’s own infrastructure.
Conflating sovereignty with security. Data security and data sovereignty are related but distinct. Security controls protect data from unauthorized access. Sovereignty controls determine who has legal authority to access data. You can have excellent security and still have sovereignty violations — if your security-compliant cloud infrastructure is operated by a foreign entity subject to disclosure obligations under its home country’s law.
Starting with technology rather than governance. Deploying a data catalog or a cloud data loss prevention tool is not a sovereignty program. Technology enables governance; it does not substitute for it. The governance processes — data classification, stewardship, architecture review, vendor management — must be designed and resourced before the technology can be effective.
The Strategic Opportunity in Data Sovereignty
It is easy to frame data sovereignty entirely in terms of compliance burden — regulations to navigate, fines to avoid, infrastructure costs to incur. That framing is incomplete and ultimately counterproductive.
Organizations that treat sovereignty as a design principle rather than an afterthought are building capabilities that create competitive advantage: the ability to enter and operate in new markets with confidence, the ability to demonstrate data trustworthiness to customers and regulators, the ability to adapt as requirements change without crisis-mode remediation, and the ability to leverage data for AI and analytics without the legal and reputational risk of sovereignty violations.
In procurement contexts, demonstrated sovereignty compliance is increasingly a differentiator. Government contracts, healthcare contracts, and financial services partnerships all require it. The ability to say credibly that you know where your data is, who can access it, and how it is governed is valuable in any regulated industry.
Customer trust is the long-term strategic asset at stake. Data sovereignty violations do not just produce regulatory fines — they produce headlines that damage brand reputation and erode the customer trust that is foundational to digital business. The organizations that win in the long run are those that customers trust with their data, and that trust is built through genuine sovereignty governance, not through compliance theater.
The enterprises that established sovereignty foundations in 2024 and 2025 are already better positioned to operate in the 2026 regulatory environment than those treating it as a 2026 project. The window to do this proactively rather than reactively is closing.
Where to Start: A Practical Action Plan
If you are reading this as a practitioner who needs to move from understanding to action, here is a starting framework.
Phase one: Establish your baseline. You need to know where you are before you can navigate to where you need to be. Conduct a data sovereignty inventory: identify your key data categories, map their jurisdictions of origin, identify the regulatory frameworks that apply, document where data is stored and processed, and identify your key data processors and their sovereignty profiles. This will produce a gap list. That gap list is your program backlog.
Phase two: Establish governance. Build the cross-functional sovereignty team. Define data classification standards that incorporate sovereignty dimensions. Establish the architecture review process that gates new data flows through sovereignty assessment. Define stewardship roles and responsibilities. Document your policies.
Phase three: Address critical gaps. Prioritize remediation based on regulatory risk and business impact. High-risk gaps — data in the wrong jurisdiction, inadequate vendor contracts, missing audit logs — get addressed first. Technical debt remediation, legacy system migration, and supply chain governance improvements take longer and need to be sequenced thoughtfully.
Phase four: Operationalize and sustain. Build sovereignty into operational rhythms: regular vendor reassessments, ongoing data map maintenance, architecture review participation, regulatory change monitoring. Establish metrics that allow you to track your sovereignty posture over time. Brief executive leadership and the board on sovereignty risk as part of regular data governance reporting.
The Bottom Line
Data sovereignty is not a trend that will peak and recede. The forces driving it — regulatory expansion, geopolitical data competition, the architectural complexity of cloud, and the growth of AI — are structural and accelerating.
For what is data governance practitioners, sovereignty is no longer a specialty topic that belongs to legal counsel alone. It is a core dimension of enterprise data governance that requires technical depth, regulatory literacy, cross-functional coordination, and executive sponsorship.
The organizations that will navigate this environment successfully are those that approach sovereignty as what it is: a fundamental question of who controls your data, under which legal regime, and with what accountability. Getting that answer right is both a compliance imperative and a strategic capability.
I have seen what happens when organizations get it right — smooth regulatory audits, faster market entry, stronger vendor negotiating positions, and customer trust that survives scrutiny. And I have seen what happens when they get it wrong. The gap between those two outcomes is increasingly wide, and it is entirely determined by the quality of your data governance.
Frequently Asked Questions
What is the difference between data sovereignty and data privacy?
Data privacy focuses on protecting individuals’ personal information from unauthorized access or misuse. Data sovereignty focuses on jurisdictional control over data — specifically, which country’s laws govern data and who has legal authority to access it. Data privacy is primarily about rights of individuals; data sovereignty is primarily about rights and authority of nations and organizations. They overlap significantly — GDPR, for instance, addresses both — but they are conceptually distinct. A data privacy violation occurs when personal data is accessed or used without proper authorization. A data sovereignty violation occurs when data is subject to legal authority or control that the governing framework does not sanction.
Does data sovereignty only apply to personal data?
No. Personal data has historically been the primary focus of sovereignty frameworks, but the EU Data Act and similar emerging frameworks extend sovereignty principles to industrial data, operational technology data, and non-personal data generated by connected devices. For organizations in manufacturing, energy, healthcare devices, and transportation, non-personal data sovereignty is increasingly regulated. Government and defense data sovereignty requirements cover classified, sensitive, and controlled unclassified information regardless of whether it contains personal data.
Can you achieve data sovereignty in a public cloud environment?
Yes, but it requires deliberate architectural choices that go beyond default cloud configurations. Sovereign cloud offerings from major providers — AWS European Sovereign Cloud, Azure EU Data Boundary — are designed to provide stronger sovereignty assurances than standard public cloud offerings. Customer-managed encryption keys, dedicated instances, contractual audit rights, and data residency controls all contribute to a sovereignty-conscious cloud architecture. However, sovereignty in public cloud is not automatic — it requires explicit design, contractual negotiation, and ongoing governance. For the most sensitive data categories, on-premises or private cloud infrastructure may still be the appropriate choice.
What should data governance framework frameworks include to address sovereignty?
A sovereignty-aware enterprise data governance framework should include: data classification standards with explicit sovereignty dimensions; a data map that captures jurisdiction of origin, storage locations, processing locations, and applicable regulatory frameworks; vendor and supply chain sovereignty assessment processes; architecture review gates that evaluate sovereignty implications of new data flows; cross-border transfer management processes; incident response procedures for sovereignty violations; and ongoing regulatory monitoring capabilities. The framework should also include clear accountability — designated roles with sovereignty governance responsibilities and the authority to enforce sovereignty requirements.
How does data sovereignty affect AI initiatives?
AI systems that process personal data are subject to existing data sovereignty frameworks — GDPR, PIPL, LGPD, and other applicable laws. The EU AI Act adds risk-based governance requirements for high-risk AI systems that create additional data documentation and auditability obligations. Practically, AI projects need to go through sovereignty review at design time: training data must be assessed for sovereignty compliance, inference data processing must respect applicable jurisdictional constraints, and audit trails must be maintained. Federated learning and privacy-enhancing technologies offer emerging approaches for sovereignty-compliant AI across jurisdictions.
Clinton Jones is a Senior Data Governance Engineer with hands-on implementation experience at Wells Fargo, the Department of Veterans Affairs, and Nestle Purina. His work spans Collibra, Profisee, and the Azure ecosystem, with deep expertise in MDM, data cataloging, and regulatory compliance. He writes about data governance practice at thedatagovernor.info.